After lots of years of using different photo organization packages, from the lovely (but expensive) Lightroom Classic to ACDSee Photo Studio, from Gallery to various manual things, I’ve mostly settled on Apple Photos on macOS. It seems to work well, handles pretty much every format under the sun, does the basic editing tasks that I use, and is sufficiently widely used to have good community support.
Because I use an Android phone and eschew public cloud provider backups there’s was no clear path for automatically importing importing the pictures I take to Apple Photos. But, it’s possible, and this writeup is to show shows the toolchain I use to do it.
The end result is that whenever I’m home I take a photo and it almost immediately appears in Photos. Or when I’m away and get back home, they automatically sync. Or if I am away for a while and want to sync my photos, I can VPN to home and sync. (I could make it sync from anywhere automatically, but I don’t yet because it gets really complicated when potentially uploading large amounts of data on mobile data, often in areas of poor connectivity.)
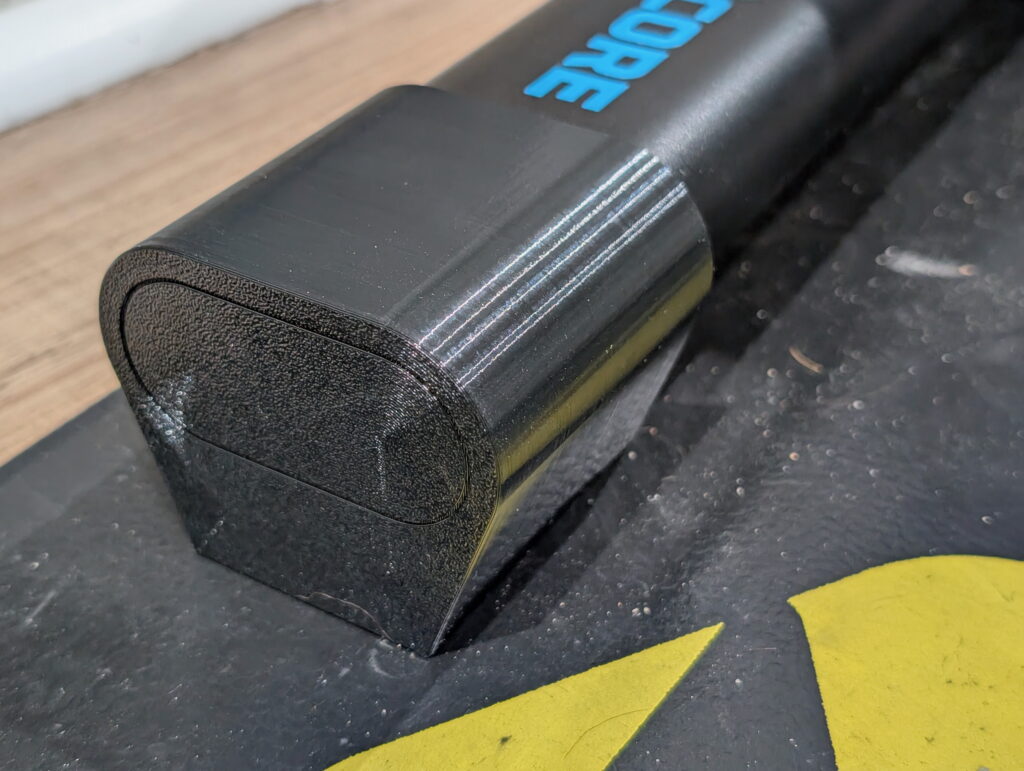
What I settled on was using FolderSync on Android to send the photos to a temporary (Inbox) folder on my NAS via SFTP. I then have Hazel watch this folder for newly arrived files, import them to Apple Photos, adding to a New Photos album, and finally putting a copy of the original in an archive folder.
Here’s how I configured this:
NAS / macOS
Due to the number of different NAS’ out there configuration of them is beyond the scope of this post, but in general what you need is a SFTP destination that’s accessible via your local network. I also then have the same area available via SMB to my Mac, and this share mapped automatically at login.
On here I’ve created two directories .../Pixel Backup/Sync Inbox/Camera which is the inbox for photos from the phone and .../Pixel Backup/Archive/Camera as a final, archival resting place for outside of what gets imported into Apple Photos, as a just-in-case backup.
(Using a separate folder for a new photo inbox radically improves performance of Hazel, because it then doesn’t have to watch a ~26GB / ~6000 file directory for changes.)
FolderSync
Create a folderPair (v2) to back up /storage/emulated/0/DCIM/Camera/ (Left account) to /Share/Pixel Backup/Inbox/Camera on my NAS via SFTP (Right account).
Under Scheduling, set a schedule for every 30 minutes, with Use WiFi checked, and limited to my home network under Allowed WiFi names. Under Sync options, check Instant sync and Only resync source files if modified (ignore target deletion).
The result of this is that when I’m home, within seconds of taking a photo, it appears on my NAS in .../Pixel Backup/Sync Inbox/Camera. Or when I’m away and take photos they’ll back up within 30 minutes of getting home.
(Yes, it’s possible to have FolderSync use SMB, but I prefer SFTP, so that’s how I set it up.)
Hazel
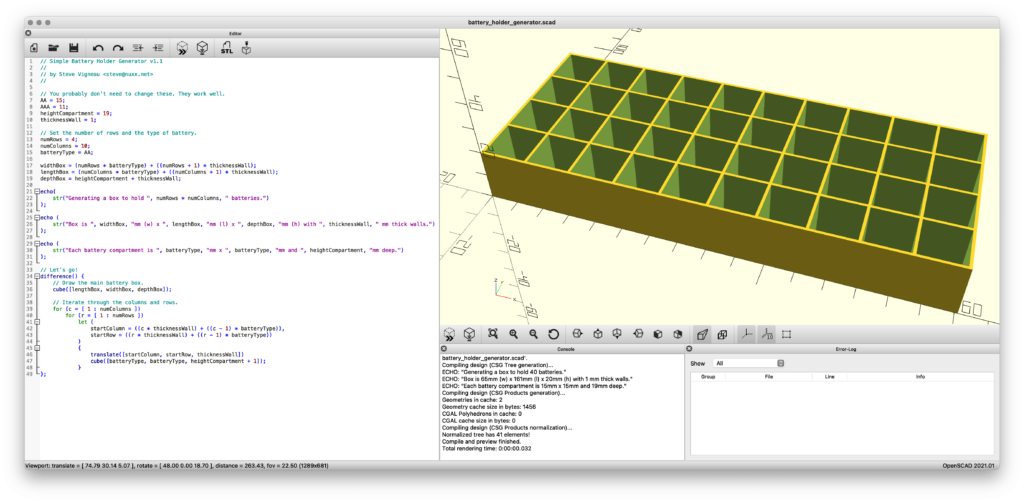
Create a Hazel rule to watch .../Pixel Backup/Sync Inbox/Camera for new files and import them into Photos:
If All of the following conditions are met
Extension is not tacitpart
Name does not start with .pending
Date Last Modified is not in the last 10 minutes
Do the following to the matched file or folder:
Import into Photos to album: New Photos
Move to folder: Camera
Files that are incompletely transferred (in flight or had an error) will have a .tacitpart extension if sync’d with a v1 folderPair, or will begin with .pending if a v2. This rule ensures that only complete files are processed, imports them into a new album called New Photos, and then moves them to .../Pixel Backup/Archive/Camera.
The 10 minute delay is needed because otherwise, Hazel will sometimes import a partially-written file resulting in a partial or corrupt image. This manifests as either a series of errors in Apple Photos about importing duplicates or the same photo imported multiple times, but incomplete, with the lower portion of the image corrupt and replaced with solid gray. (This delay could probably be reduced, but for now I’m using 10 minutes. I may reduce this in the future.)
(Note: I tried syncing photos into a single folder and having Hazel watch that for changes, but performance was very poor. I’m unsure of whether this was caused by using it over a network, it’s size, or the number of files to be parsed, although based on Hazel’s performace on a very full Download folder I suspect the latter. I didn’t bother to investigate further, as using the Sync Inbox architecture works out better, and makes it easier to troubleshoot and recover if something goes awry.)
Apple Photos
Apple Photos has a library containing all images, and these images may or may not be assigned to one or more albums.
My preferred workflow is to have individual albums for select projects, trips, or whatnot, and all other mobile phone images in a general Mobile Photos album. To facilitate this, Hazel puts all new photos from my phone into a New Photos album. I then periodically look at this album, sort the photos into the desired other albums, and then remove them from this album. (Or, sometimes, delete them entirely.)
While I could have everything just go into the main pool of photos, they are somewhat unsorted, and dependent on metadata or parsing of the image content itself for sorting For personal reasons I like to have each photos in an album of some sort, and I find that this inbox of sorts best matches how I like to manage my photos.
But the best thing is that photos I take using my phone while working on projects at home are immediately available in Photos and then backed up. And those taken while away get uploaded immediately upon returning or by connecting to VPN and telling FolderSync to sync immediately, “…on any available network connection”.
That’s It!
And, that’s that. I take photos on my phone, they automatically appear in Photos and get archived on my NAS, and then backed up. Effective, yet simple to use.
For what it’s worth, I also have some other sync tasks in FolderSync and Hazel to handle screenshots, images attached to or saved from messages (SMS, Google Chat, Facebook Messenger, Signal, etc), but it’s all done with similar flows to what’s above, so I’m not going to document them separately.
Update on 2025-Jun-20
I previously had issues with Photos where the Memories, Trips, and Featured Photos sections just didn’t work. All of these indicate that I need to add more photos, but I’ve got some 64,000 photos spanning 20+ years of EXIF dates and locations, and the People & Pets, Map, Handwriting, and Illustration sections/detections work fine, so I don’t think it’s an issue with quantity nor the ability to parse the photos. This was fixed at some point between when I originally wrote the article in late January 2025 and now.
Since writing the article I also ran into some issues with partial syncing of files, especially when the wireless connection was poor and copying was slow, so I added another rule to Hazel so it won’t sync files newer than 10 minutes which seems to have taken care of it.