(UPDATE: With the release of Synology DSM 7.0 this setup will break. It’s easy to fix and I’ve updated added this post describing how to make this system work under the new version.)
Lately I’ve become enamored with BorgBackup (Borg) for backups of remote *NIX servers, so after acquiring a Synology DS1019+ for home I wanted to make it the destination repository for Borg-based backups of nuxx.net. While setting up Borg is usually quite straightforward (a package or stand-alone binary), it’s not so cut and dry on the Synology DiskStation Manager (DSM); the OS which runs on the DS1019+ and most other Synology NAS’.
What follows here are the steps I used to make and the reason for each step. In the end it was fairly simple, but a few of the steps are obtuse and only relevant to DSM.
These steps were written for DSM 6.2.2; I have not checked to see if it applies to other versions. Also, I leave out all details of setting up public key authentication for SSH as this is thoroughly documented elsewhere.
- Enable “User Home Service” via Control Panel → User → Advanced → User Home → Enable user home service: This creates a home directory for each user on the machine and thus a place to store
.ssh/authorized_keysfor the backup user account. - Create a backup user account and make it part of the administrators group: Accounts must be part of administrators in order to log in via SSH. Starting with DSM 6.2.2 non-admin users do not have SSH access.
- Change the permissions on the backup user’s home directory to 755: By default users’ home directories have an ACL applied which has too broad of permissions and SSH will refuse to use the key, instead prompting for a password. Home directories are located under
/var/services/homesand this can be set viachmod 755 /var/services/homes/backupuser. (See this thread for details.) - Put
~/.ssh/authorized_keys, containing the remote user’s public key, in place under the backup user’s home directory and ensure that the file is set to 700: If permissions are too open, sshd will refuse to use the key. - Test that you can log in remotely with ssh and public key authentication.
- Place the borg-linux64 binary (named
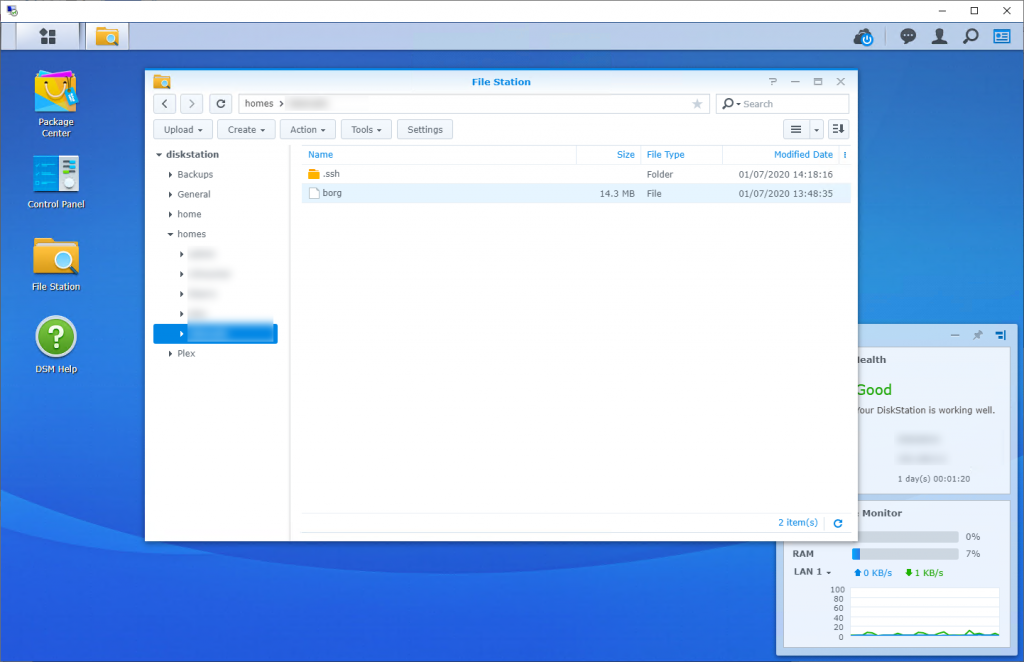
borg) in the user’s home directory and confirm that it’s executable: Binaries available here. - Create a directory on the NAS to be used the backup destination and give the backup user read and write permissions.
- Modify the backup user’s
~/.ssh/authorized_keysto prevent remote interactive logins and restrict how borg is run: This is optional, but a good idea.
In this example only theborg servecommand (the borg repository server) can be run remotely, is restricted to 120GB of disk, in a repository on DSM under the backup directory of/volume2/Backups/borg, and from remote IP of 192.168.0.23:command="/var/services/homes/backupuser/borg serve --storage-quota 120G --restrict-to-repository /volume2/Backups/borg",restrict,from="192.168.0.23" ssh-rsa AAAA[...restofkeygoeshere...] remoteuser@remoteserver.example.com
Please note, there are a number of articles about enabling public key authentication for SSH on DSM which mention uncommenting and setting PubkeyAuthentication yes and AuthorizedKeysFile .ssh/authorized_keys in /etc/ssh/sshd_config and restarting sshd. I did not need to do this. The settings, as commented out, are the defaults and thus already set that way (see sshd_config(5) for details).
At this point DSM should allow a remote user, authenticating with a public key and restricted to a particular source IP address, to use the Synology NAS as a BorgBackup repository. For more information about automating backups check out this article about how I use borg for backing up nuxx.net, including a wrapper script that can be run automatically via cron.
Comments closed